“Whenever you do a thing, act as if all the world were watching.” – President Thomas Jefferson
Introduction
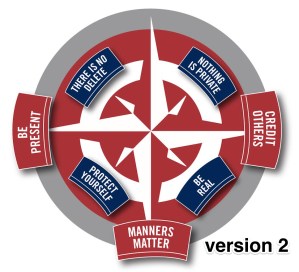
 Every application and app has a delete feature. There is typically a reassuring trash can icon sitting conveniently close by waiting for us to remove anything no longer needed. A delete key on every keyboard gives the false sense of security that the elimination of offending material, silly posts, angry messages, old files, and more can simply and easily be wiped out of existence. The truth is there are screenshots, trash cans full of old files, cookies, search histories, and much more just below the digital surface.
Every application and app has a delete feature. There is typically a reassuring trash can icon sitting conveniently close by waiting for us to remove anything no longer needed. A delete key on every keyboard gives the false sense of security that the elimination of offending material, silly posts, angry messages, old files, and more can simply and easily be wiped out of existence. The truth is there are screenshots, trash cans full of old files, cookies, search histories, and much more just below the digital surface.
Leaving a Mark
As we all know students of all ages tend to be creatures of the “here and now”. Long term planning and delayed consequences are difficult for our students to envision. We all know that this can impair decision making and technology can add additional complexities at times. Control of information and images is difficult to manage when users have so many ways to capture content. We cannot rely on a “undo” or “delete” option in the digital environment.
 For example, a student is excited about getting their driver’s license and decides to post a photo of their new license. To the student, it seems harmless. It is only shared with their “friends” (See earlier chapter on nothing is private). However, we, as adults, understand that there is significant risk to sharing this personal information. Removing the picture from their account is easy, but students often fail to see once posted they lose control of the ownership of the picture. So, help your students to pause before posting and consider the following about images.
For example, a student is excited about getting their driver’s license and decides to post a photo of their new license. To the student, it seems harmless. It is only shared with their “friends” (See earlier chapter on nothing is private). However, we, as adults, understand that there is significant risk to sharing this personal information. Removing the picture from their account is easy, but students often fail to see once posted they lose control of the ownership of the picture. So, help your students to pause before posting and consider the following about images.
Obviously, not all jokes are funny and many rely on body language, tone, and inflection which can be subtle. Students need to be able to play with humor, explore what their community finds funny, and learn from their mistakes. The digital space is not very forgiving because it lacks the subtlety of face to face interaction. Combine these reasons with the speed at which information can be shared online and you have a recipe for mistakes with the potential for widespread, lingering impact. Teachers and parents can help students by coaching them to pause before posting and ask the questions below.
 It is important for our students to act as though there is no delete especially while they are fine tuning their sense of humor, posting images, and sharing online.
It is important for our students to act as though there is no delete especially while they are fine tuning their sense of humor, posting images, and sharing online.
Next are two examples to help students think about living like there is no delete. First, watch the video about a teenager who made international news capturing the attention of L’oreal only to quickly losing her modeling career because of an Instagram post.
Next, read the story of current UNC Tarheel and former Charlotte Catholic running back, Elijah Hood. The important element of his story is that even though he delete his Vine video, you can still find a copy of the video on YouTube. The video on Youtube is posted by SB Nation Sports Writer.
Things you should Know about Digital Trash:
- Cookies can be bad or how cookies can impact your experience online
- Websites you visit collect information about you
- Even your school work tracks your changes and progress
- Your thoughts captured by simple two button process – Android or Apple
-
-
-
- we know you know it is that easy….but why do you keep forgetting?
- why aren’t you worried about screen captures of your posts?
-
-
-
- How hard is it to recover deleted files?
Take Action
Our use of digital tools has two layers, a public one that anyone can search using Google, Bing, or other search engines, and a less visible one that leaves a trail of digital breadcrumbs someone can use to find you and find out much about you. Teachers and students need to know about both layers, and strategies to help maintain a positive digital footprint.
Your public digital footprint. Talk with students about he fact that everything you post online can be captured, preserved, and searched. Hopefully the ideas that “there is no delete” causes each of us to reflect on whether we want what we share to live forever.
If you share something online you regret, here are some actions to take:
- Delete it as soon as possible.
- Search for the deleted “shared item”. Can you still find it?
- If it is an image, use a Reverse Google Image Search to to try to find the picture. This may tell if the image is being shared somewhere else.
- Apologize if you hurt someone feelings, shared something they didn’t want share, or insulted someone.
If you send something via email that you regret, here are some actions to take:
- Apologize. Be specific and accept responsibility for your actions. Don’t send another email explaining your actions unless the person you offended asks why.
- Get an trusted adult involved if you are unclear about how to resolve the problem.
- Remember that even if you were trying to be funny, it is up to the person receiving the email to determine how it made them feel.
Discuss with your students or even role play how to communicate with adults. Help students understand that the casual way that interact with friends is not appropriate for communicating with their teachers.
Your hidden digital footprint. Every website and phone/tablet/computer communicate with each other, and often leave  records behind. Some of these records can be deleted, others cannot. Look for opportunities to remind students of their invisible “digital breadcrumbs”.
records behind. Some of these records can be deleted, others cannot. Look for opportunities to remind students of their invisible “digital breadcrumbs”.
Review these terms to know with your students.
Cookies– Small pieces of data collected and kept by a website about you. Often they are used to remember choices you made last time you used the site, but they can also collect information about you for the site owner.
Internet history– The list of sites visited kept by your internet browser – Safari, Chrome, Firefox. This list can be used to see where and when a user visited webpages.
Search history – The list of keywords used on search engines. Your search history can help you find a website you searched for in the past and it can be used to determine which advertisements you might want to see.
Metadata – This term describes information stored in other files about the files themselves. For example, digital pictures store location information, date, and time in the file that includes the image. Ever wonder how your computer knows when you took your pictures? How does it create albums based on events? It uses metadata.
Ultimately, “there is no delete” is simply a statement to help us understand that once we share we lose control of the content we share. Share wisely.
How do you take action? Share your ideas here.
Lesson plans, resources, & more
Grades K-2: Follow the Digital Trail
Students learn that the information they put online leaves a digital footprint or “trail.” This trail can be big or small, helpful or hurtful, depending on how they manage it.
Grades 4-12 Building Your Digital Footprint
Creative interactive image that helps students learn more about their digital footprint.
Grades 6-8: Trillion Dollar Footprint
Students learn that they have a digital footprint and that this information can be searched, copied and passed on, but that they can take some control based on what they post online.
Grades 6-12 The Really Long Infographic on Online Privacy
This infographic is a wonderful tool for facilitating discussion with your students. What would they change? What did they learn from reviewing the graphic?
Students learn that everything they or anyone else posts about them online becomes part of a public online presence known as a digital footprint.
General Interest: Social Media after Death
Article discussed new laws regarding access to social media accounts after someone dies.